UPDATE (3-15-19): Cyberscoop identifies the three countries to which Cyber Command sent operatives last November.
Nakasone did not name the countries. But a Cyber Command spokesperson said two of those countries were the Balkan nations of Montenegro and North Macedonia, which until February was known as Macedonia. And a U.S. government official with knowledge of the matter said the third country was Ukraine – something corroborated by a public statement from a top Defense Department official.
“We’ve been conducting some defensive cyber operations with some of our partners in Europe,” Burke “Ed” Wilson, the deputy assistant secretary of defense for cyber policy, told Signal Magazine in January. “It’s the first time we’ve actually had teams on networks in Macedonia, Montenegro and Ukraine, for starters.”
Cyber Command’s midterm election work included trips to Ukraine, Montenegro, and North Macedonia (Cyberscoop)
Defense Department and Homeland Security officials warn Russia did try to interfere in the 2018 election, and the United States is not prepared for what foreign adversaries likely will launch in 2020.
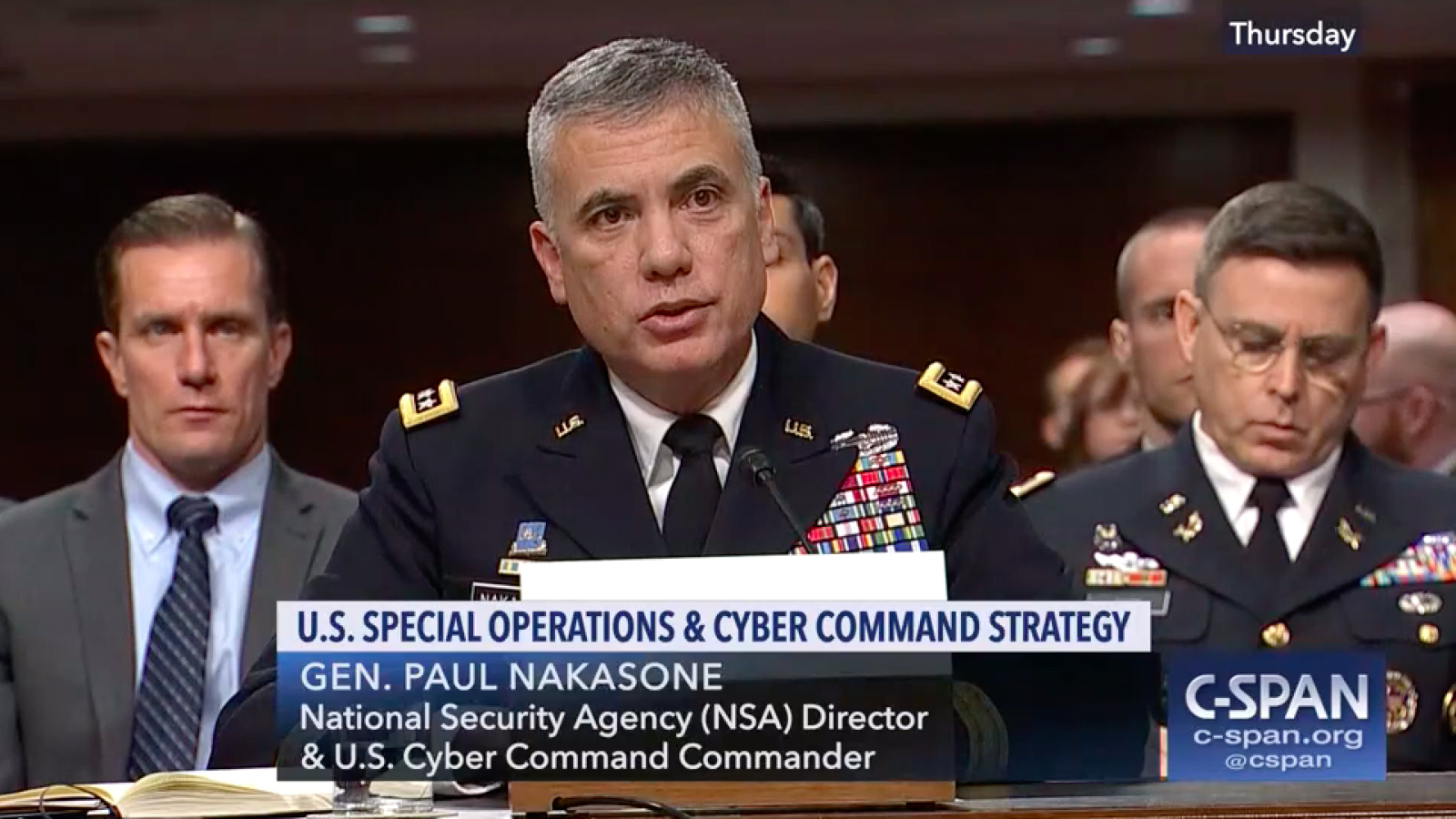
Army Gen. Paul Nakasone, head of U.S. Cyber Command, laid out the escalating threats, following a Navy review released this week that described significant breaches of naval systems and concluded that the service is losing the cyber war.
Speaking during a subcommittee hearing, Nakasone said the U.S. is now prepared to use cyber operations more aggressively to strike back, as the nation faces growing cyberattacks and threats of interference in the 2020 presidential elections.
He said the military learned a lot working with other government agencies to thwart Russian interference in the 2018 midterm elections, and the focus now has turned to the next election cycle.
(...)
Members of Congress peppered Nakasone and Kenneth Rapuano, the assistant defense secretary for homeland defense, with questions about what the military is doing to respond to cyber breaches and deter countries like Russia and China.
Rapuano acknowledged that for years the U.S. did not sufficiently respond to cyberattacks by other nations, particularly as the breaches did not rise to the level of a conventional military response. He said deterrence is about imposing consequences and, “historically we have not done that.”
CNN:
"US Cyber Command, working in partnership with the National Security Agency, provided indicators of compromise to the Federal Bureau of Investigation and the Department of Homeland Security," Nakasone told lawmakers on the House Armed Services Committee's Subcommittee on Cybersecurity in testimony Wednesday.
Nakasone also said Cyber Command moved "defensive teams" last November to three countries in Europe. The US official said the teams were sent to three Eastern European countries but declined to say which ones.
In December 2018, Director of National Intelligence Dan Coats said Russia, China and Iran sought to influence the midterm elections, but that the US had no intelligence reporting "that indicates any compromise of our nation's election infrastructure" that would have disrupted voting.
CNN:
Department of Homeland Security Cybersecurity and Infrastructure Security Agency Director Chris Krebs told lawmakers on the House Appropriations Homeland Security Subcommittee that "what keeps him up at night" is thinking about the new ways adversaries will attempt to infiltrate US election systems in 2020.
"I know what they did in '16. I know that they tried to do in '18. What will they do in 2020?" Krebs asked. "That's what keeps me up at night."
Krebs said that the best way to defend against unknown threats is to "make sure we are covering down on the basics" and engaging with the American public.
"We have to let them know there are bad people out there who try to do bad things but we've got a system here that works," he said.
(...)
Krebs also highlighted the need for some states to transition to election systems that allow for the results to be audited, noting that five states are of particular concern because they don't have voter paper trails: South Carolina, Georgia, Louisiana, New Jersey and Delaware.
"My primary focus would be get them off of those machines onto something that leads to an auditability outcome," he said.
The proposed budget released on Tuesday calls for a 10 percent increase in Pentagon spending on cyber operations, for a total of $9.6 billion.
US warns of sophisticated cyberattacks from Russia, China (AP)
Russia sought to interfere with US election systems in 2018 midterms, US official says (CNN)